In today’s threat landscape, cyberattacks leveraging compromised credentials now cause over 80% of breaches annually. Whether via password spraying attacks, phishing lures, or dark web data dumps, attackers routinely gain access to stolen usernames and passwords. Even complex machine-generated passcodes eventually get exposed.
This undermines legacy perimeter defenses reliant on single-factor authentication – typically static usernames and passwords.
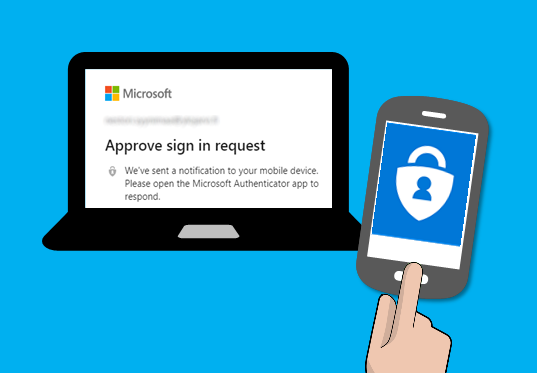
In response, multi-factor authentication (MFA) has rapidly become essential for robust security across modern IT environments. MFA adds critical redundancy at point of access by requiring two or more verification methods before granting user sign-ins into applications, devices and networks.
Whether paired factors like a password plus a one-time code or combining biometrics, security keys and trusted devices, MFA instantly neutralizes risks from compromised credentials. Two factors mean attackers need to compromise both an account password AND capture a secondary factor token/biometric live during the access attempt. The probability of this drops exponentially.
As this guide will explore, a wide spectrum of MFA solutions now exist tailored to securing Windows infrastructure specifically. Leading options for safeguarding on-premises Windows Server 2016 domains and Windows 7/8/10 clients alongside Microsoft 365 joined endpoints include:
– Microsoft Azure AD Multi-Factor Authentication
– Duo Beyond VPN for Windows
– RSA SecurID Access for Windows Logon
– YubiKeys for Windows Login
For Windows environments, the imperative now lies in evaluating organizational risk tolerance, infrastructure complexity and budget to dictate the optimal MFA adoption strategy. The capabilities exist – the next step is implementation.
MFA Solutions for Windows Platforms
Purpose-built for Microsoft environments, Azure Active Directory Multi-Factor Authentication seamlessly covers Windows Server 2016 and Windows 7/8/10 clients via cloud-based identity services. Conditional access policies secure sign-ins while self service password reset portals enhance user productivity.
Duo Security’s Windows Logon Integration provides on-premises MFA for RDP sessions, Outlook Web Access and other Windows apps. Expanding protection beyond cloud SSO and VPN connections, Duo interoperates with Active Directory for convenient domain logins.
Yubico offers the YubiKey bio-USB security key for low-cost MFA hardware across Windows platforms. Tapping the key after login generates a one-time password, while integrated fingerprints enable biometric authentication.
Additional options like RSA SecurID provide robust on-premises MFA as well but typically necessitate more IT administration overhead. Cloud platforms simplify operational management for Windows users and devices through economies of scale.
Configuring MFA for Windows: Best Practices
When implementing multifactor authentication (MFA) across Windows devices and servers, following core best practices sets the foundation for driving adoption and realizing sustained value:
Require MFA for Administrators and Privileged Users:
– Enforce blanket MFA policies for all users with elevated permissions to access sensitive systems and data.
– This could encompass domain admins, server admins, service accounts, DBAs and more.
Securing External Access Points:
– Mandate MFA on VPNs, Outlook Web Access, WiFi networks and other external access channels to validate identities before granting network entry rights.
Balance Security and Productivity via Risk-Based Policies:
– Rely on adaptive machine learning and risk-based policies to limit unnecessary MFA friction during benign access attempts.
– Prompt MFA challenges during risky scenarios like foreign travel or password changes.
Support Multiple Verification Options:
– Allow end users to select amongst verification methods like biometrics, one-time passcodes, SMS texts or security keys based on preferences.
– This avoids overdependence on any singular channel.
Provide Self-Service Password Reset:
– Implement self-service portals coupled with MFA for user-driven password resets.
– This offloads volume from IT help desks to resolve credential issues swiftly.
Proper configuration and policy tuning provides a tailored framework for MFA success across the Windows environments. And consistent user education regarding MFA processes cements understanding required for productive long-term usage.
Top Multi-Factor Authentication Products
| Product | Description |
| Cisco Secure Access by Duo | MFA with adaptive risk profiling for Windows & other platforms |
| IBM Verify | Robust on-prem MFA supporting various Windows authentication methods |
| LastPass MFA | Cost-effective cloud-based MFA included with premium password manager |
| Microsoft Azure AD MFA | Cloud MFA with broad OS support & robust access policies |
Windows Hello for Business: An Advanced MFA Solution
Windows Hello for Business brings integrated biometric authentication for supported Windows 10/11 devices through fingerprint, facial or iris recognition sign-ins. Combined with a second factor like a one-time passcode, this passwordless approach secures Windows while eliminating cumbersome PINs and passwords.
Multi-device authentication allows users to approve sign-ins from a trusted secondary device as the second factor. And backing Windows Hello, Azure AD Multi-Factor Authentication automates policy prompts after initial logins for sustained protection.
Challenges and Solutions for Implementing Windows MFA
Despite immense security upside, MFA adoption sees roadblocks like:
| Challenge | Solution |
| User friction impacting productivity | Balance security with convenient verification options like biometrics and security keys alongside education on MFA benefits |
| Integration complexity with legacy systems | Leverage adaptable gateways like RADIUS and modern protocols like OAuth 2.0 and OpenID Connect for interoperability |
| Cost concerns limiting deployment | Prioritize high-impact users/systems for initial MFA coverage then expand over time as budgets allow |
Through planning and partnerships with mature MFA vendors, organizations can overcome obstacles to institute robust protection.
Integration complexity with legacy systems
Leverage adaptable gateways like RADIUS and modern protocols like OAuth 2.0 and OpenID Connect for interoperability
Cost concerns limiting deployment
Prioritize high-impact users/systems for initial MFA coverage then expand over time as budgets allow
Through planning and partnerships with mature MFA vendors, organizations can overcome obstacles to institute robust protection.
Integrating MFA with Existing Windows Systems
To maximize returns on investment, multi-factor authentication (MFA) solutions must seamlessly integrate with existing infrastructure and directories maintaining identities and access controls.
From legacy VPN concentrators to modern identity providers (IdPs) like Active Directory, most leading MFA platforms provide flexible integration methods:
RADIUS and LDAP:
- RADIUS protocol serves as a common gateway for securing legacy VPNs, routers and other niche appliances lacking native MFA support.
- Lightweight LDAP plugins allow querying user attributes from AD for policy assignments.
This maintains backwards compatibility while delivering stronger MFA security.
SAML and OAuth 2.0:
- SAML and OAuth 2.0 represent modern standards for facilitating single sign-on (SSO) across cloud apps and services.
- MFA platforms integrate as middleware, enabling identity federation from Windows client SSO to cloud apps.
This maintains seamless user experiences across Windows 10 to Microsoft 365 while prompting MFA when necessary.
Active Directory Pass Through Authentication:
- MFA servers capture Windows logins then pass credentials through to Active Directory for validation, maintaining convenient AD credential roaming.
- This password vaulting prevents additional on-boarding friction.
Custom Integrations:
- Custom plugins, agents and toolkits allow interoperation with niche legacy systems as needed.
- Crawlers can auto-discover apps lacking other integration options.
Lastly, user education around MFA details, security benefits and simple enrollment/usage processes helps further facilitate frictionless adoption across Windows users.
Multi factor authentication for windows login – join.
By blending standards-based federation with customization options as required, organizations can institute pervasive MFA without necessitating disruptive rip-and-replace projects as part of Windows security enhancement initiatives.
Finding Cost-Effective Windows MFA Solutions
While robust multifactor authentication unquestionably delivers immense security value, cost considerations can still impede adoption by resource-constrained organizations.
Fortunately, several compelling cost-saving options exist for securing Windows infrastructure via MFA:
Microsoft 365 Plans:
– Microsoft bundles Azure AD Multi-Factor Authentication into premium bundles like Microsoft 365 Business Premium and E5 at no additional user charges.
– This grants MFA for all federated users under conditional access policies.
Identity Partner Capabilities:
– Leading identity partners like Okta often include limited multifactor authentication into base user charges.
– For example, Okta may bundle SMS and soft token verification for all users then charge only for advanced methods like biometrics or hardware keys.
MFA Vendor Free Tiers:
– Most dedicated MFA platforms like Duo Security offer free tiers for smaller user pools. Many also provide trial licenses to demonstrate value.
– While limited, this allows basic MFA coverage for high-risk users to partially mitigate risk.
Additionally, prioritizing more affordable MFA methods can maximize coverage for budget-limited organizations:
– One-time passcodes via SMS and authenticator apps minimizes costs
– U2F security keys cost ~$20 per user providing high ROI
– Windows Hello biometrics leverages built-in resources
Getting started with basic MFA can deliver massive security gains and build internal support for expanded investments over time.
In total, a little creativity and vendor engagement can often uncover flexible, cost-effective methods for significantly enhancing Windows security through multifactor authentication.
Conclusion: MFA Offers Vital Windows Server and Desktop Security
With stolen passwords contributing to over 80% of confirmed breaches annually, adopting MFA represents a foundational security step for Windows Server and client platforms—instantly expanding identity assurance. As this guide has shown, robust options exist to facilitate Windows MFA rollout from leading identity vendors. Now is the time to evaluate business risk tolerance and invest in commensurately stronger access controls through multifactor authentication.
Frequently Asked Questions
Q: Is on-premises MFA better than cloud MFA for Windows? A: Not universally – leading SaaS MFA often outperforms on-prem in ease of use and automation.
Q: Does Windows Server natively support biometrics? A: Not yet – Windows Server lags behind Windows 10/11 in native biometric authentication capabilities currently.
Q: What is the most secure MFA method for Windows? A: Security keys providing FIDO2/WebAuthn authentication likely represent the most secure MFA approach for supported Windows platforms.
Q: How does MFA integrate with Active Directory?
A: Solutions typically integrate via RADIUS or leverage lightweight AD agents to bridge communication securely.
Q: Can users bypass MFA prompts on Windows? A: With sufficient admin rights users can disable MFA agents – underscoring the importance of coupling technical controls with testing and education.

Kaushal Joshi is a versatile author with expertise in web development and technical writing. With a passion for both coding and effective communication, Kaushal has forged a dynamic career at the intersection of technology and content creation. His proficiency in web development is complemented by a talent for articulating complex technical concepts in clear and accessible language. Through his writing, Kaushal not only contributes to the evolving field of web development but also empowers readers with the knowledge to navigate the digital landscape. His commitment to bridging the gap between technology and understanding makes Kaushal Joshi a respected figure in both the web development and technical writing communities.
Leave a Reply